Hardcoding secrets = big mistake.
API keys, passwords, tokens — if leaked, your entire system is at risk.
This guide shows how to manage secrets properly.
What Are Secrets?
- API keys
- Database passwords
- SSH keys
- Tokens
The Problem
Bad practice:
const API_KEY = "123456789";If this leaks → you’re exposed.
Best Practices
1. Use Environment Variables
export API_KEY=your_secretAccess:
process.env.API_KEY2. Use .env Files (Local Only)
DB_PASSWORD=secret123⚠️ Never commit .env to Git.
3. Use Secret Managers
Best tools:
- HashiCorp Vault
- AWS Secrets Manager
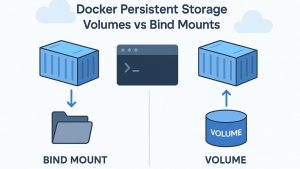
- Docker Secrets
- Kubernetes Secrets
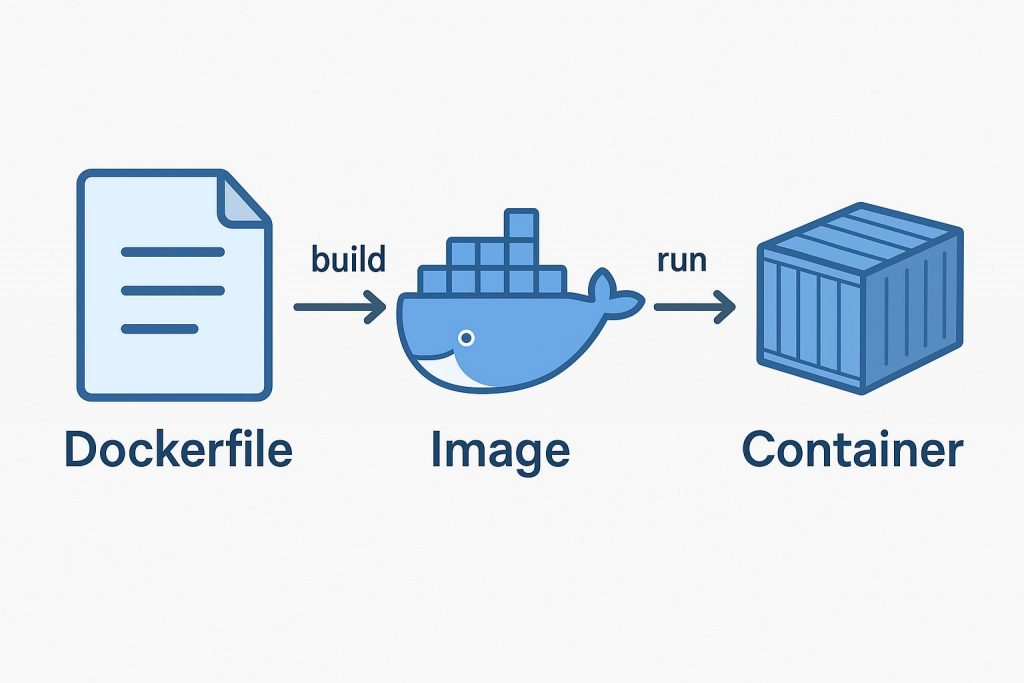
Example: Docker Secrets
echo "mypassword" | docker secret create db_password -Example: Kubernetes Secret
kubectl create secret generic my-secret \
--from-literal=password=mypasswordWhy It Matters
- Prevent data breaches
- Secure infrastructure
- Required in production
Common Mistakes
❌ Hardcoding secrets
❌ Committing .env files
❌ Sharing keys in Slack
❌ No rotation policy
Pro Level Tips
- Rotate keys regularly
- Use short-lived tokens
- Limit access permissions
- Audit usage logs
Final Thoughts
Security in DevOps is not optional.
👉 Treat secrets like passwords — because they are.